University of Wisconsin Under Fire for Admitting Student Tied to $46 Million Crypto Fraud Network, Doxbin, and Multiple Public Safety Threats
The University of Wisconsin has a problem on its hands — and they’re refusing to do a damn thing about it.
MADISON, Wis. — An investigation has revealed that a future University of Wisconsin student maintained deep ties to a federal cryptocurrency fraud suspect, held a staff position on one of the internet's most notorious harassment platforms, and was at the center of multiple public safety emergencies — raising urgent questions about what the university knew and when.
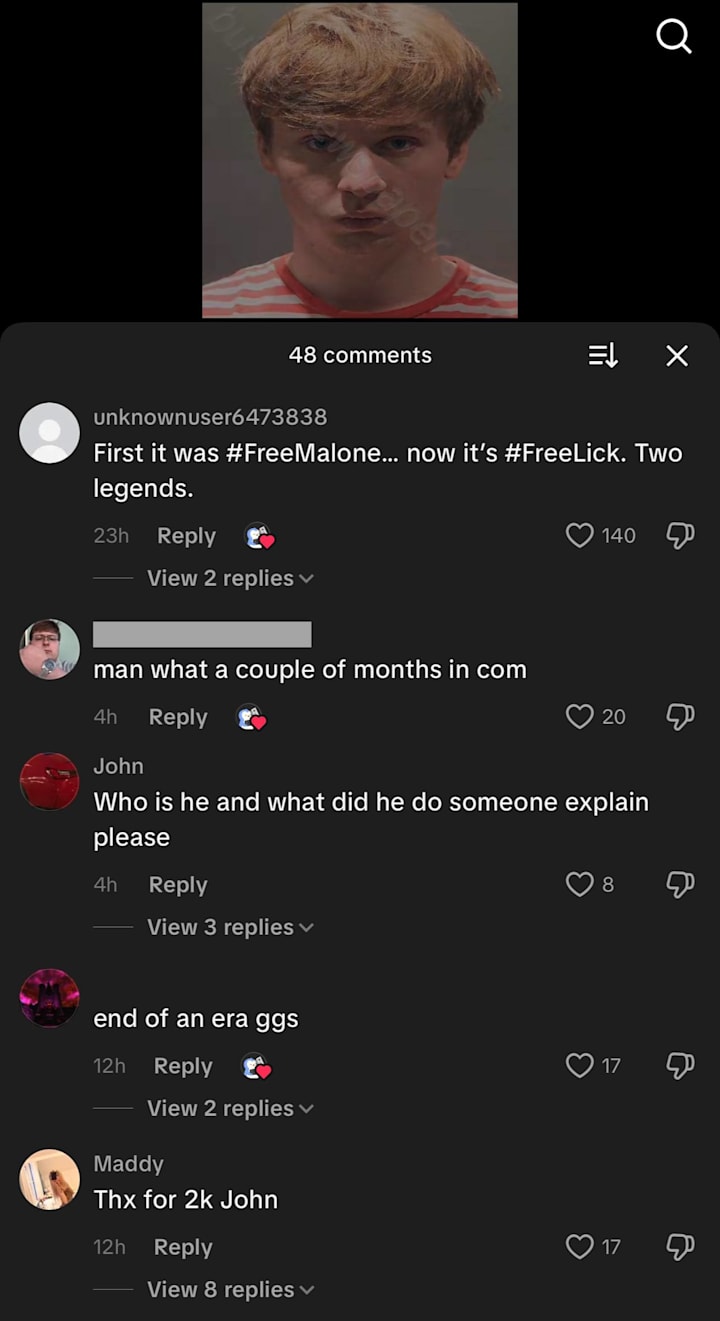
Maddy Jacquinot, listed as a member of the Class of 2030 according to her public Instagram biography, has been linked through documents, screenshots, and multiple corroborating sources to John Daghita, a federal contractor now accused of stealing approximately $46 million in cryptocurrency through elaborate social engineering schemes. The two reportedly met through Minecraft servers and Telegram channels frequented by individuals involved in fraud-oriented communities.

We has reviewed leaked screenshots showing conversations between Jacquinot and Daghita that reference active cryptocurrency scam operations. Several of the exchanged messages also contain racist language. Jacquinot's social media footprint further reveals that she follows Dritan Kapllani, a known social engineer with his own documented history within online fraud circles, on Instagram — a connection multiple sources describe as more than coincidental.
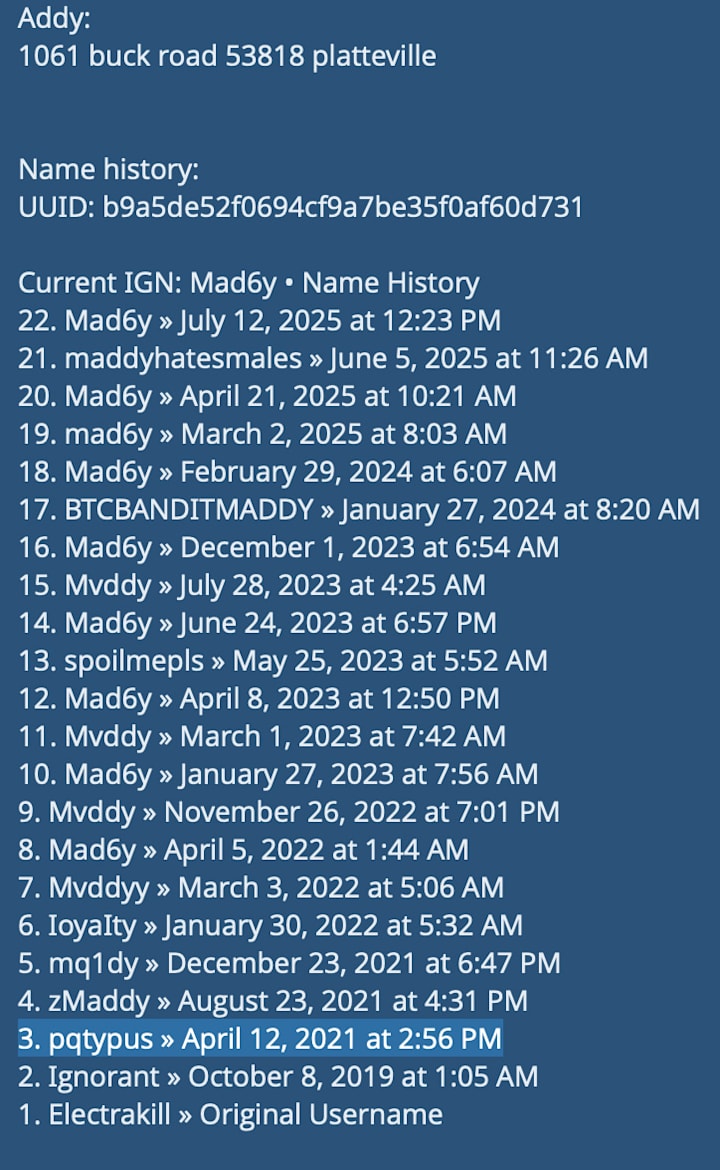
Perhaps most telling is the digital alias trail. Jacquinot previously operated under the handle "BTCBANDITMADDY" — a username whose prefix, BTC, refers to Bitcoin, and whose inclusion of "bandit" needs little interpretation. The alias has appeared across multiple platforms connected to cryptocurrency fraud discussions.
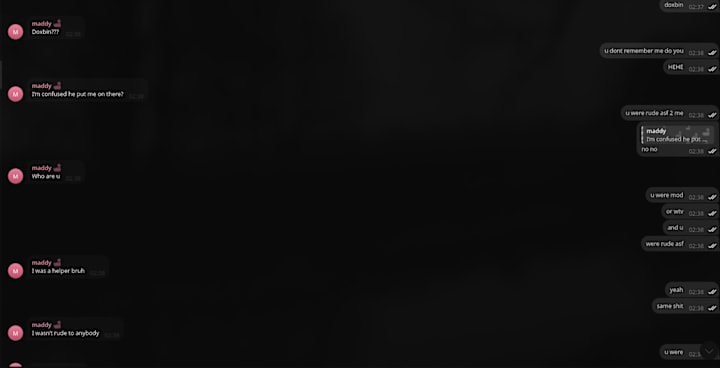
Multiple independent sources have confirmed to us that Jacquinot was involved in an online romantic relationship with the owner of Doxbin, a website widely recognized by law enforcement and cybersecurity researchers as a hub for facilitating doxxing, swatting, and targeted harassment campaigns.
During the course of that relationship, Jacquinot reportedly held a staff role on the platform under the username "pqtypus" — an alias that matches her known Xbox gamertag and other online accounts. That staff position granted her elevated access to the site's operations, including user data and posting capabilities on a platform the FBI has repeatedly flagged in connection with real-world violence.
After the relationship ended, sources say she was reassigned a vanity role labeled "rich" — still listed under the same alias, still visible to Doxbin's user base.
The consequences of Jacquinot's online affiliations have not remained digital.
In late October 2025, a hoax swatting call was placed to her residence — a tactic extensively documented within the Telegram fraud communities she frequented, where swatting serves as retaliation against rivals or former associates. Law enforcement responded in force to a fabricated emergency, diverting resources and endangering everyone inside the home and in the surrounding neighborhood.
Weeks later, in December 2025, Platteville High School received a bomb threat that disrupted the entire school's operations. Investigators linked the threat back to Jacquinot's online persona and her visibility within these same communities. The school did not have school the next day. The Grant County Sheriffs office investigated it.
Both incidents consumed significant local law enforcement resources and generated widespread fear across the Platteville community — a community that includes families, children, and elderly residents who had nothing to do with Telegram fraud channels or cryptocurrency theft.
We contacted the University of Wisconsin administration requesting comment on Jacquinot's enrollment status, whether the institution had been made aware of her connections to federal fraud suspects, her role on a known harassment platform, or the public safety incidents that preceded her enrollment.
When asked if they would take any action against Jacquinot or investigate these serious allegations further university officials responded: “We are not planning on taking any disciplinary action at this time.”
Public records, social media posts, and news coverage of the Platteville bomb threat and swatting incident were available well before the 2026 a began. Jacquinot's Instagram — publicly accessible, listing her class year and university affiliation — sits alongside follows of known social engineers. Her aliases are searchable. The Doxbin connection is documented across multiple cybersecurity forums and archived discussions. None of this information was buried. None of it required a subpoena to find.
The question is not whether the university could have known. The question is whether an institution responsible for the safety of thousands of students, faculty members, and staff exercised even minimal due diligence before welcoming onto its campus an individual whose online footprint is entangled with a $46 million fraud case, a harassment platform linked to real-world violence, and two separate incidents that required emergency response from local law enforcement.
Universities routinely screen applicants for far less. Social media audits have become standard practice in admissions offices across the country. A simple Google search of Jacquinot's name, her known aliases, or the Platteville incidents would have surfaced red flags that no responsible admissions committee could reasonably ignore.
Taken individually, each element of Jacquinot's history might warrant a conversation. Taken together — the documented communication with a man accused of stealing $46 million, the staff role on a platform the FBI associates with swatting and harassment, the aliases that reference cryptocurrency theft, the bomb threat that shut down a high school, the swatting call that sent armed officers to a residential address, the financial transactions thanked publicly on TikTok, the association with known social engineers — the picture is not ambiguous.
Parents sending tuition checks deserve to know what safety protocols exist when an admitted student's background includes connections to federal-level criminal investigations. Faculty deserve to know whether their classrooms could become targets of the same retaliatory tactics — swatting, bomb threats, doxxing — that followed Jacquinot through high school.
The University of Wisconsin has an obligation that extends beyond enrollment numbers and tuition revenue. Every institution of higher learning accepts a duty of care the moment it issues an acceptance letter. When the publicly available evidence connecting a prospective student to fraud networks, harassment infrastructure, and community-endangering incidents is this extensive, admission without investigation is not an oversight. It is a choice.





Comments
There are no comments for this story
Be the first to respond and start the conversation.